Understanding Encryption: Securing Sensitive Information Online
Understanding Encryption: Securing Sensitive Information Online
In our increasingly digital world, the need for robust data protection has never been more critical. Every day, we share sensitive information online, from personal banking details to private communications. Understanding encryption is fundamental to safeguarding this data, transforming readable information into an unreadable format to prevent unauthorized access. It acts as a digital lock, ensuring that only intended recipients with the correct key can unlock and view the content. This article will demystify encryption, exploring its core principles, various types, and practical applications for securing sensitive information online.
Key Points:
- Encryption Basics: Learn how data is scrambled and protected.
- Types of Encryption: Differentiate between symmetric and asymmetric methods.
- Daily Applications: Discover encryption in HTTPS, VPNs, and messaging.
- Best Practices: Adopt strategies for stronger digital security.
- Future Trends: Explore the evolving landscape of cryptographic challenges.
The Fundamentals of Encryption: How it Works to Secure Data
At its core, encryption is the process of converting information or data into a code to prevent unauthorized access. This process, known as cryptography, involves transforming plaintext (readable data) into ciphertext (unreadable, encrypted data) using an algorithm and a key. The strength of the encryption largely depends on the complexity of the algorithm and the length and randomness of the key. Without the correct decryption key, the ciphertext remains unintelligible, effectively securing sensitive information online.
Imagine sending a secret message. Instead of writing it plainly, you use a complex cipher known only to you and the recipient. This is the essence of encryption. The algorithm is the set of rules for scrambling the message, and the key is the specific piece of information that makes the scrambling unique. For example, a common encryption standard like AES-256 uses a 256-bit key, making it incredibly difficult for even powerful computers to crack through brute force. This robust protection is why encryption is indispensable for online privacy and data integrity.
Exploring Different Types of Encryption for Online Security
While the goal of all encryption is to protect data, various methods are employed depending on the context and security requirements. Two primary types dominate the landscape: symmetric and asymmetric encryption. Each plays a vital role in understanding encryption and its applications.
Symmetric Encryption: Speed and Simplicity
Symmetric encryption uses a single, shared secret key for both encrypting and decrypting data. This method is generally faster and more efficient, making it suitable for encrypting large volumes of data. Examples include the Advanced Encryption Standard (AES), widely used for file encryption and secure communications. The challenge with symmetric encryption lies in securely exchanging the shared key between parties. If the key falls into the wrong hands, the security of the entire communication is compromised.
Asymmetric Encryption (Public Key Cryptography): Secure Key Exchange
Asymmetric encryption, also known as public-key cryptography, uses a pair of mathematically linked keys: a public key and a private key. The public key can be freely shared, used to encrypt data, but cannot decrypt it. Only the corresponding private key, kept secret by its owner, can decrypt the data. This ingenious system solves the key exchange problem inherent in symmetric encryption. RSA is a prominent example of an asymmetric algorithm, often used for secure key exchange and digital signatures. This dual-key approach is crucial for establishing secure connections, such as those used by HTTPS.
End-to-End Encryption (E2EE): Ultimate Privacy
End-to-End Encryption (E2EE) is a system where only the communicating users can read the messages. No third party, not even the service provider, can access the plaintext content. This is achieved by encrypting data on the sender's device and decrypting it only on the recipient's device. E2EE is a powerful application of both symmetric and asymmetric encryption working in tandem, offering the highest level of online privacy for communications. Many popular messaging apps now offer E2EE by default, a significant step forward in securing sensitive information online.
Practical Applications of Encryption in Daily Digital Life
Encryption isn't just for spies or top-secret government communications; it's an integral part of our everyday digital interactions. From browsing the web to sending emails, encryption works silently in the background to protect our data.
- HTTPS for Secure Web Browsing: When you see "HTTPS" in your browser's address bar and a padlock icon, it means your connection to that website is encrypted. This uses Transport Layer Security (TLS), which relies on asymmetric encryption to establish a secure channel and then switches to symmetric encryption for faster data transfer. This protects your login credentials, credit card numbers, and other data submitted through web forms. For a deeper dive into web application security best practices, readers can explore related articles on secure coding.
- Virtual Private Networks (VPNs): VPNs create an encrypted tunnel between your device and a VPN server, masking your IP address and encrypting all your internet traffic. This is particularly useful when using public Wi-Fi networks, which are often insecure, preventing eavesdropping and ensuring your digital protection.
- Email Encryption: While not all email is encrypted by default, services like ProtonMail or features like PGP (Pretty Good Privacy) allow for end-to-end encrypted email communication. This ensures that the content of your emails remains private, even from your email provider.
- Cloud Storage and Messaging Apps: Reputable cloud storage providers encrypt data both in transit and at rest. Similarly, many modern messaging applications, as mentioned, offer E2EE, ensuring your chats and media are private.
Best Practices for Implementing Robust Encryption and Digital Protection
While encryption technology is powerful, its effectiveness largely depends on how it's implemented and used. Adopting best practices is crucial for maximizing your online security.
- Use Strong, Unique Passwords: Encryption keys are often protected by passwords. A weak password is the weakest link, making even the strongest encryption vulnerable. Use a password manager to generate and store complex, unique passwords for all your accounts.
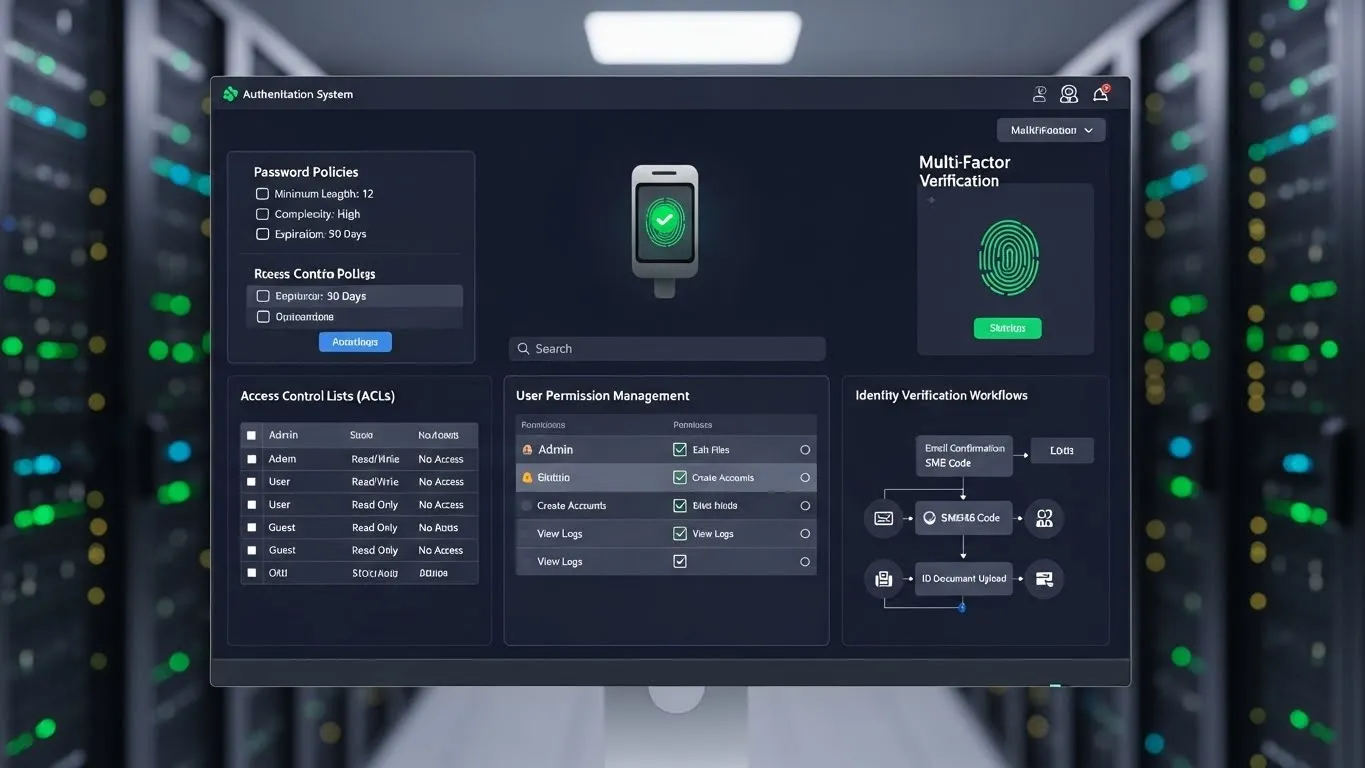
- Enable Two-Factor Authentication (2FA): 2FA adds an extra layer of security by requiring a second form of verification (e.g., a code from your phone) in addition to your password. This significantly reduces the risk of unauthorized access, even if your password is compromised.
- Keep Software Updated: Software updates often include critical security patches that fix vulnerabilities. Regularly updating your operating system, browsers, and applications ensures you benefit from the latest digital protection measures.
- Understand Privacy Policies: Before using a service, take time to understand its privacy policy. Does it use end-to-end encryption? How is your data handled? Being informed empowers you to make better choices for securing sensitive information online.
- Be Wary of Public Wi-Fi: Public Wi-Fi networks are often unsecured, making your data vulnerable. Always use a VPN when connecting to public networks to encrypt your traffic and protect your privacy.
From my experience in web application security, the weakest link often isn't the encryption algorithm itself, but its implementation or user behavior. Even the most advanced encryption can be bypassed if a user falls for a phishing scam or uses a predictable password.
The Evolving Landscape of Digital Security and Encryption
The field of cryptography is constantly evolving, driven by advancements in computing power and the emergence of new threats. One significant area of research and concern is the potential impact of quantum computing on current encryption standards. Many of today's asymmetric encryption algorithms, like RSA, could theoretically be broken by sufficiently powerful quantum computers.
This has led to intense research in post-quantum cryptography (PQC), which aims to develop new encryption algorithms resistant to quantum attacks. Organizations like the National Institute of Standards and Technology (NIST) are actively working to standardize these new algorithms, a critical step for future data security. According to a 2024 report by Cybersecurity Ventures, global cybercrime costs are projected to reach $10.5 trillion annually by 2025, underscoring the critical role of encryption and the need for continuous innovation. The ongoing development of robust, quantum-resistant encryption will be vital for securing sensitive information online for decades to come.
Another emerging trend is the increasing focus on homomorphic encryption, which allows computations to be performed on encrypted data without decrypting it first. This technology holds immense promise for privacy-preserving cloud computing and data analytics, enabling organizations to gain insights from data without ever exposing the raw, sensitive information. To understand more about protecting your personal data, consider reviewing our resources on online privacy.
Frequently Asked Questions (FAQ) about Encryption
Q1: What is the primary purpose of encryption?
The primary purpose of encryption is to protect the confidentiality and integrity of digital information. By transforming data into an unreadable format, encryption ensures that only authorized individuals with the correct decryption key can access and understand it. This prevents unauthorized access, tampering, and eavesdropping, making it essential for securing sensitive information online across various applications and services.
Q2: Is all encryption equally secure?
No, not all encryption is equally secure. The strength of encryption depends on several factors, including the algorithm used, the length of the encryption key, and the quality of its implementation. Older or weaker algorithms, shorter keys, or flawed implementations can make encrypted data vulnerable to attacks. Modern, robust standards like AES-256 are considered highly secure, but even these require proper usage and regular updates to maintain their effectiveness.
Q3: How can I tell if a website uses encryption?
You can easily tell if a website uses encryption by looking at its URL in your web browser. If the address begins with "HTTPS" (Hypertext Transfer Protocol Secure) and displays a padlock icon next to it, the connection is encrypted. This indicates that any data you send to or receive from that website is protected by TLS/SSL encryption, significantly enhancing your online security while browsing.
Q4: Can encrypted data ever be recovered without the key?
While theoretically possible through brute-force