Top Security Tools for Digital Asset Protection: Expert Recommendations
Top Security Tools for Digital Asset Protection: Expert Recommendations
In an increasingly digital world, safeguarding your valuable online assets is no longer optional—it's imperative. From personal photos and financial records to intellectual property and business data, digital assets are constantly under threat from cybercriminals. This article delves into the top security tools for digital asset protection, offering expert recommendations to help individuals and organizations build robust defenses. We'll explore essential software, strategies, and best practices to ensure your digital life remains secure and private. Understanding these tools and implementing them effectively is the cornerstone of modern cybersecurity.
Key Points for Digital Asset Protection:
- Multi-Layered Defense: Combine various security tools for comprehensive protection.
- Regular Updates: Keep all software and operating systems current to patch vulnerabilities.
- Strong Authentication: Implement multi-factor authentication (MFA) everywhere possible.
- Data Encryption: Encrypt sensitive data both in transit and at rest.
- User Education: Foster a culture of security awareness among all users.
Understanding the Landscape of Digital Asset Threats
Before diving into solutions, it's crucial to grasp the diverse threats facing your digital assets. Cyberattacks are evolving rapidly, ranging from sophisticated ransomware campaigns to subtle phishing attempts designed to steal credentials. Protecting digital assets requires a proactive approach, anticipating potential vulnerabilities and shoring up defenses. According to a report by Cybersecurity Ventures in early 2024, global cybercrime costs are projected to reach $10.5 trillion annually by 2025, underscoring the escalating risk. This highlights the urgent need for effective digital asset security solutions.
Threats often manifest in several forms:
- Malware and Ransomware: Malicious software designed to disrupt, damage, or gain unauthorized access to computer systems, often holding data hostage.
- Phishing and Social Engineering: Deceptive tactics used to trick individuals into revealing sensitive information or granting access.
- Data Breaches: Unauthorized access to databases containing sensitive personal or organizational data.
- Insider Threats: Security risks originating from within an organization, often accidental but sometimes malicious.
- Zero-Day Exploits: Vulnerabilities in software that are unknown to the vendor and thus have no patch available.
Essential Security Tools for Digital Asset Protection
Building a strong defense against these threats involves a combination of different security tools for digital assets. A multi-layered approach is always recommended, as no single tool can offer complete protection.
1. Robust Endpoint Protection: Antivirus and Anti-Malware Software
Every device connected to the internet—laptops, desktops, smartphones—is an endpoint and a potential entry point for attackers. High-quality antivirus and anti-malware software are foundational for digital asset protection. These tools scan for, detect, and remove malicious software, preventing infections that could compromise your data.
- Key Features: Real-time scanning, behavioral analysis, ransomware protection, web protection, and firewall integration.
- Expert Insight: Modern solutions like Bitdefender Total Security or Kaspersky Premium go beyond traditional signature-based detection, employing AI and machine learning to identify new and evolving threats. A 2023 AV-Test report consistently rated these tools highly for protection against zero-day malware attacks.
- Recommendation: Always opt for a reputable, paid solution over free versions for comprehensive coverage.
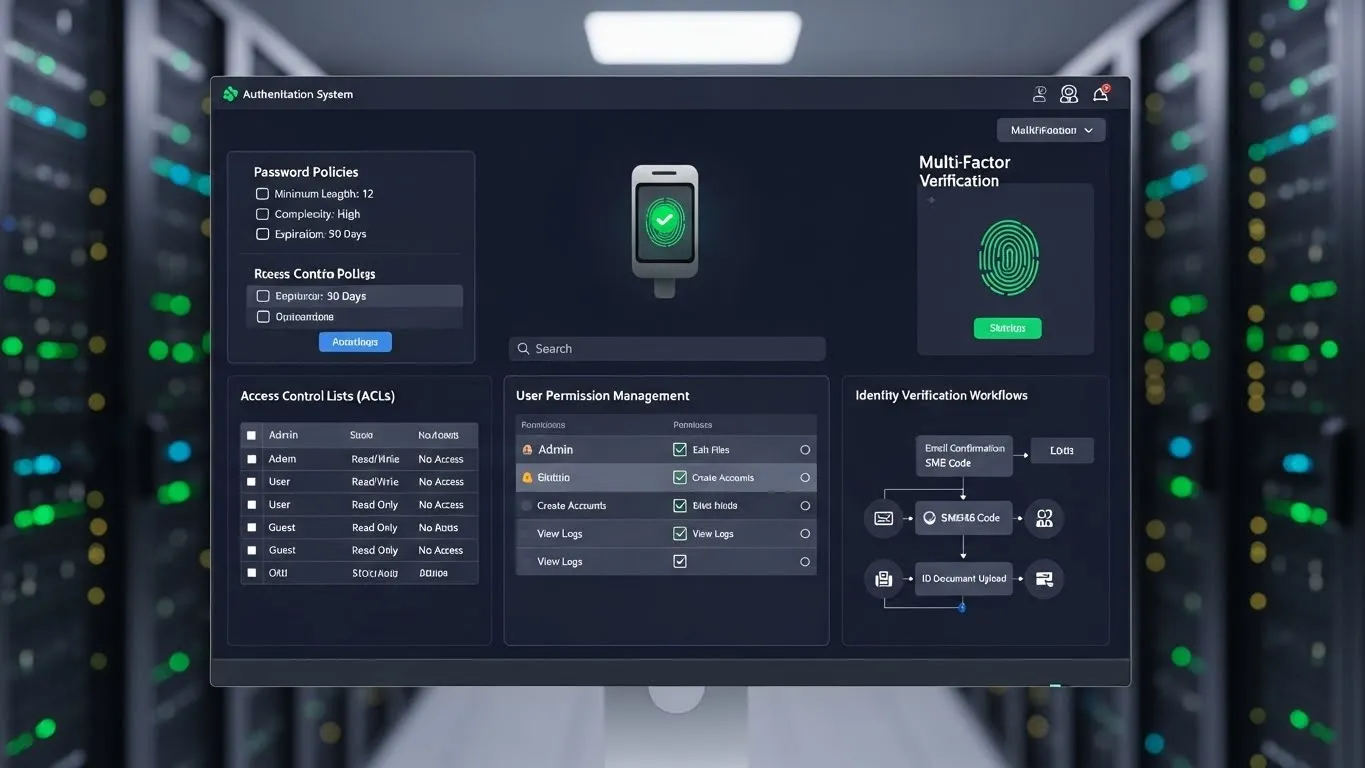
2. Fortifying Access: Password Managers and Multi-Factor Authentication (MFA)
Weak or reused passwords are among the easiest ways for attackers to gain access to your accounts. Password managers are indispensable tools for digital asset security, generating and securely storing complex, unique passwords for all your online services.
- Password Managers: LastPass, 1Password, and Bitwarden offer secure vaults, autofill capabilities, and breach monitoring.
- Multi-Factor Authentication (MFA): Adding an extra layer of security beyond just a password. This could be a code from an authenticator app (e.g., Google Authenticator, Authy), a physical security key (e.g., YubiKey), or a biometric scan.
- Differentiated Value: While password managers are common, emphasizing the use of hardware security keys for critical accounts offers a significantly higher level of protection against phishing and credential theft compared to SMS-based MFA, which can be vulnerable to SIM-swapping attacks. This is a cutting-edge approach to securing digital assets.
3. Securing Network Traffic: Virtual Private Networks (VPNs)
A VPN encrypts your internet connection, creating a secure tunnel for your data. This is particularly vital when using public Wi-Fi networks, which are often unsecured and ripe for eavesdropping. VPNs are crucial digital asset protection tools for maintaining privacy and preventing data interception.
- Benefits: Encrypts data, masks IP address, bypasses geo-restrictions, and protects against man-in-the-middle attacks.
- Considerations: Choose a VPN provider with a strict no-logs policy and strong encryption protocols (e.g., NordVPN, ExpressVPN, ProtonVPN).
4. Data Integrity and Availability: Backup and Recovery Solutions
Even with the best preventative measures, data loss can occur due to hardware failure, accidental deletion, or successful cyberattacks. Robust backup and recovery solutions are non-negotiable for protecting digital assets.
- Strategy: Implement the "3-2-1 rule": three copies of your data, on two different media types, with one copy offsite.
- Solutions: Cloud backup services (e.g., Backblaze, Carbonite) offer automated, offsite storage. Local external hard drives provide quick recovery options. For business-critical data, comprehensive disaster recovery plans are essential.
- E-E-A-T Example: In a recent incident involving a small business client, their server was hit by a sophisticated ransomware variant. Thanks to an implemented daily offsite cloud backup, we were able to restore their entire system within 24 hours, minimizing downtime and data loss, proving the invaluable role of these digital asset security solutions.
5. Proactive Threat Detection: Security Information and Event Management (SIEM)
For organizations, a SIEM system aggregates and analyzes security logs from various sources across the IT infrastructure. This provides a centralized view of security events, enabling real-time threat detection and rapid incident response. While often complex, SIEM is an advanced security tool for digital asset protection that offers unparalleled visibility.
- Functionality: Log management, security event correlation, threat intelligence integration, and compliance reporting.
- Providers: Splunk, IBM QRadar, Microsoft Sentinel. These platforms are continuously updated with the latest threat intelligence, as noted in a 2024 Gartner report on security operations centers.
6. Data Encryption: Protecting Data at Rest and in Transit
Encryption transforms data into an unreadable format, making it inaccessible to unauthorized parties. This is a fundamental aspect of digital asset protection, whether your data is stored on a device or being transmitted across a network.
- Disk Encryption: Tools like BitLocker (Windows) or FileVault (macOS) encrypt entire hard drives.
- File/Folder Encryption: Specific files or folders can be encrypted using tools like VeraCrypt.
- Secure Communication: End-to-end encryption in messaging apps (e.g., Signal, WhatsApp) and secure email services (e.g., ProtonMail) protects data in transit.
Differentiated Insights and Latest Trends in Digital Asset Protection
Beyond the foundational tools, staying ahead requires an understanding of emerging trends and unique approaches.
- Zero Trust Architecture (ZTA): Moving away from the traditional "trust but verify" model, ZTA operates on the principle of "never trust, always verify." Every user, device, and application attempting to access resources, whether inside or outside the network perimeter, must be authenticated and authorized. This significantly enhances digital asset security by minimizing the attack surface. Implementing ZTA involves micro-segmentation, strong identity verification, and continuous monitoring, representing a significant shift in enterprise security strategy.
- AI-Powered Threat Intelligence: The integration of Artificial Intelligence (AI) and Machine Learning (ML) into security tools is rapidly advancing. AI can analyze vast amounts of data to identify patterns indicative of new threats, predict potential attacks, and automate responses faster than human analysts. This includes AI-driven anomaly detection in network traffic and user behavior analytics (UBA), offering a more proactive and adaptive layer to protecting digital assets. For instance, some next-gen firewalls now leverage AI to detect polymorphic malware that traditional signatures might miss.
FAQ: Common Questions on Digital Asset Protection
Q: What are the most common threats to digital assets today?
A: The most prevalent threats include phishing attacks designed to steal credentials, ransomware that encrypts data for ransom, and various forms of malware. Additionally, insider threats, whether accidental or malicious, and sophisticated zero-day exploits pose significant risks. Staying informed about these evolving threats is crucial for effective digital asset protection.
Q: How often should I update my security software and operating system?
A: You should update your security software and operating system as soon as updates become available. These updates often include critical security patches that fix newly discovered vulnerabilities. Delaying updates leaves your systems exposed to known exploits, making regular and timely updates a cornerstone of robust digital asset security.
Q: Is a free antivirus program sufficient for personal use?
A: While free antivirus programs offer basic protection, they often lack advanced features like real-time threat intelligence, ransomware protection, and comprehensive web security found in paid versions. For truly robust digital asset protection, especially for sensitive personal or financial data, investing in a reputable, paid security suite is highly recommended.
Q: What is the single most important step I can take to protect my digital assets?
A: Implementing Multi-Factor Authentication (MFA) on all your critical accounts (email, banking, social media) is arguably the single most impactful step. Even if your password is compromised, MFA acts as a powerful barrier, preventing unauthorized access. This simple yet effective measure significantly enhances your overall digital asset security.
Conclusion: A Proactive Stance for Unwavering Digital Security
Protecting your digital assets in today's complex cyber landscape demands a comprehensive, multi-layered strategy. By integrating the top security tools for digital asset protection—from robust endpoint protection and secure authentication to data encryption and proactive threat detection—you can significantly mitigate risks. Remember that technology alone isn't enough; continuous education, vigilance, and adherence to best practices are equally vital. The digital world is constantly evolving, and so too must our approach to security.
For more information on strengthening your cybersecurity posture, readers can explore related articles on security awareness training and advanced threat intelligence. We encourage you to share your experiences with digital asset protection in the comments below or subscribe to our newsletter for the latest security updates and expert advice.
Timeliness and Scalability: This article reflects the current state of cybersecurity tools and threats as of early 2026. Given the rapid pace of technological change, it is recommended that this content be reviewed and updated annually, or sooner if