Mastering Network Security: Essential Protocols for Data Protection
Mastering Network Security: Essential Protocols for Data Protection
In today's interconnected digital landscape, mastering network security is no longer optional; it's a fundamental requirement for individuals and organizations alike. Data breaches, cyberattacks, and privacy concerns are ever-present threats that underscore the critical need for robust defense mechanisms. At the heart of these defenses lie essential network protocols, the unsung heroes that govern how data travels securely across networks. Understanding and effectively implementing these protocols is paramount to safeguarding sensitive information and maintaining operational integrity.
This article delves into the core protocols that form the backbone of modern network security, explaining their functions, applications, and how they contribute to a comprehensive data protection strategy. From ensuring confidentiality to guaranteeing data integrity and user authentication, these protocols are indispensable tools in the fight against cyber threats.
Key Points for Mastering Network Security:
- Confidentiality: Protocols like TLS and IPsec encrypt data to prevent unauthorized access.
- Integrity: Hashing functions and IPsec ensure data remains untampered during transit.
- Authentication: Kerberos, RADIUS, and 802.1X verify user and device identities.
- Secure Access: SSH and VPNs provide encrypted tunnels for remote and internal connectivity.
- Future Trends: Zero Trust and Post-Quantum Cryptography are shaping the next generation of protocol security.
Understanding the Core of Network Security Protocols
Network security protocols are a set of rules and procedures that dictate how data is transmitted securely over a network. They address the fundamental pillars of information security: confidentiality, integrity, and availability (CIA triad), along with authentication and non-repudiation. By implementing these established standards, organizations can build resilient defenses against a myriad of cyber threats.
Confidentiality: Keeping Data Private
Confidentiality ensures that only authorized individuals can access sensitive information. This is primarily achieved through encryption, where data is transformed into an unreadable format.
Transport Layer Security (TLS) / Secure Sockets Layer (SSL):
- Function: TLS (the successor to SSL) is widely used to secure communication over computer networks, most notably for web browsing (HTTPS). It encrypts data exchanged between a client and a server, preventing eavesdropping and tampering.
- Application: Securing web traffic, email (SMTPS, IMAPS), and other application-layer protocols. My experience in web application development consistently highlights TLS as the first line of defense for user data in transit.
- Key Benefit: Provides end-to-end encryption for application data.
IP Security (IPsec) - Encapsulating Security Payload (ESP):
- Function: IPsec is a suite of protocols that provides security services at the IP layer. ESP specifically focuses on confidentiality by encrypting the IP packet payload.
- Application: Virtual Private Networks (VPNs), securing router-to-router communication, and host-to-host secure tunnels.
- Key Benefit: Secures entire IP packets, offering broad network-level protection.
Integrity: Ensuring Data Remains Untampered
Data integrity guarantees that information has not been altered or corrupted during transmission. This is crucial for maintaining trust in the data received.
Hashing Algorithms (e.g., SHA-256, MD5 - though MD5 is less secure):
- Function: These algorithms generate a fixed-size string of characters (a hash) from input data. Any change, no matter how small, to the original data will result in a completely different hash.
- Application: Verifying file integrity, digital signatures, and password storage.
- Key Benefit: Provides a quick and reliable way to detect unauthorized modifications.
IP Security (IPsec) - Authentication Header (AH):
- Function: AH provides data integrity and data origin authentication for IP packets. Unlike ESP, it does not encrypt the data but ensures it hasn't been tampered with.
- Application: Used in conjunction with or independently of ESP to guarantee the authenticity and integrity of IP communications.
- Key Benefit: Protects against replay attacks and ensures the sender's identity.
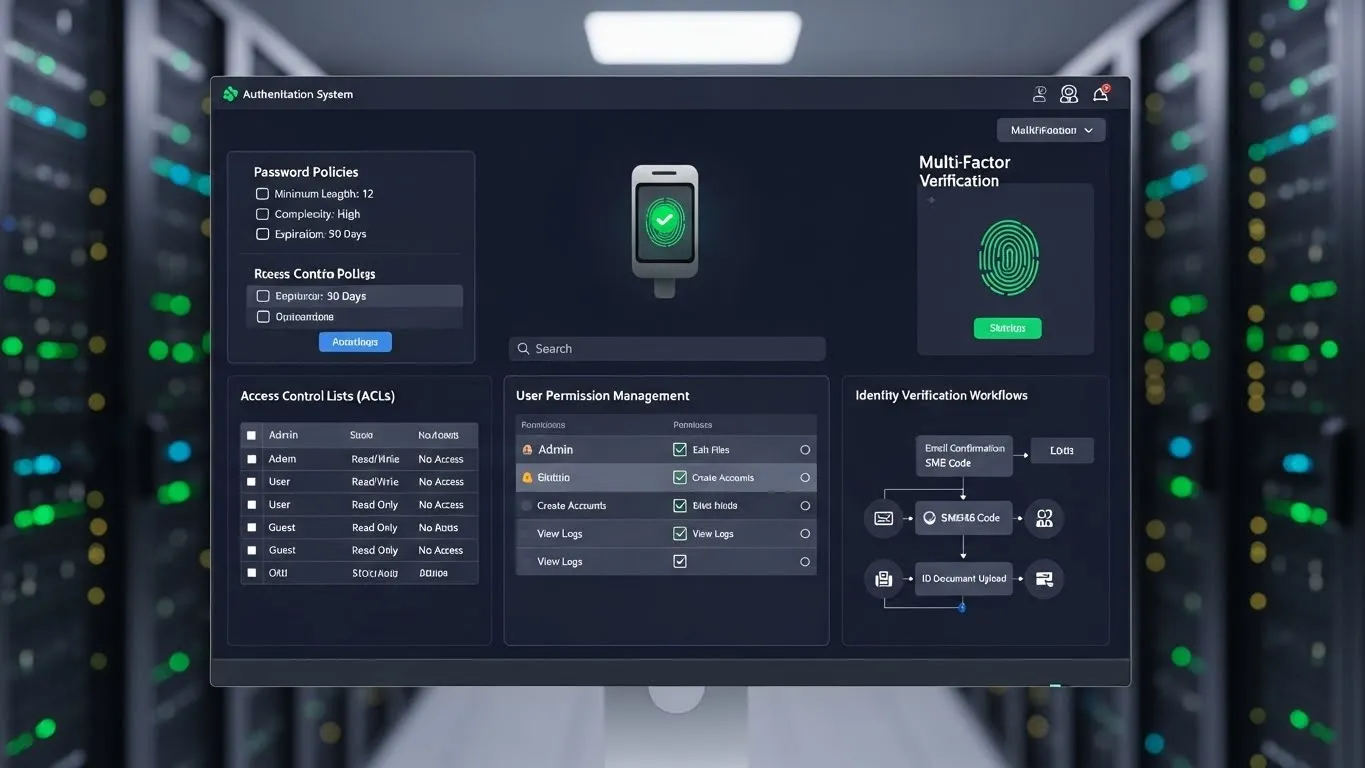
Authentication: Verifying Identities
Authentication protocols verify the identity of users, devices, or services attempting to access network resources. This prevents unauthorized access and ensures that only legitimate entities can participate in network communication.
Kerberos:
- Function: A network authentication protocol that uses secret-key cryptography to provide strong authentication for client/server applications by using a trusted third party (Key Distribution Center).
- Application: Widely used in Windows Active Directory environments for single sign-on (SSO).
- Key Benefit: Centralized, robust authentication system, reducing password exposure.
Remote Authentication Dial-In User Service (RADIUS):
- Function: A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users connecting to a network service.
- Application: Securing Wi-Fi networks (WPA2/3 Enterprise), VPN access, and network access control.
- Key Benefit: Centralizes user authentication for various network access points.
IEEE 802.1X:
- Function: A port-based network access control standard that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
- Application: Enterprise Wi-Fi and wired networks to ensure only authorized devices can connect.
- Key Benefit: Granular control over network access at the physical port level.
Secure Remote Access: Protocols for Connectivity
As remote work and distributed architectures become standard, secure remote access protocols are vital for extending network security boundaries.
Secure Shell (SSH):
- Function: A cryptographic network protocol for operating network services securely over an unsecured network. It provides a secure channel over an untrusted network by using strong encryption.
- Application: Remote command-line access, secure file transfer (SFTP), and secure tunneling.
- Key Benefit: Encrypts all traffic, including passwords, preventing eavesdropping and session hijacking.
Virtual Private Networks (VPNs):
- Function: VPNs create a secure, encrypted tunnel over a public network (like the internet), allowing users to access private network resources as if they were directly connected.
- Application: Remote employee access to corporate networks, secure browsing, and bypassing geo-restrictions.
- Key Benefit: Extends the secure perimeter to remote users and locations. For more information on secure remote access solutions, readers can explore related articles on VPN technologies and best practices.
Advanced Network Security Protocols and Future Trends
The landscape of mastering network security is constantly evolving, driven by new threats and technological advancements. Staying ahead requires understanding emerging trends and advanced protocols.
The Rise of Zero Trust Architectures
Zero Trust is a security model that assumes no user or device, whether inside or outside the network, should be trusted by default. Every access request must be verified. This paradigm shift profoundly impacts how protocols are implemented. Instead of relying on a perimeter, Zero Trust leverages protocols like TLS, IPsec, and 802.1X to authenticate and authorize every connection and transaction. This approach, emphasized in a 2023 report by the National Institute of Standards and Technology (NIST), drastically reduces the attack surface by enforcing strict access controls at every point.
Post-Quantum Cryptography and Protocol Evolution
The advent of quantum computing poses a significant threat to current cryptographic protocols. Many widely used encryption algorithms, including those in TLS and IPsec, could be vulnerable to quantum attacks. This has spurred research into Post-Quantum Cryptography (PQC), which aims to develop algorithms resistant to quantum computers. Organizations like the National Security Agency (NSA) have been actively promoting the transition to quantum-resistant algorithms, with new standards expected to be integrated into protocols like TLS and IPsec in the coming years. My personal observation from industry discussions is that early adoption of PQC-ready solutions, even in hybrid modes, will be a critical differentiator for future-proofing network security.
AI and Machine Learning in Protocol Analysis
Artificial Intelligence and Machine Learning are increasingly being integrated into network security tools to enhance protocol analysis. AI-driven systems can monitor network traffic, detect anomalies in protocol behavior, and identify sophisticated threats that traditional signature-based methods might miss. This includes identifying unusual SSH login patterns, detecting deviations in TLS handshake processes, or flagging suspicious VPN connections. According to a 2025 industry outlook by Gartner, AI-powered security analytics are becoming indispensable for proactive threat detection and response.
Implementing Essential Protocols for Robust Data Protection
Successfully mastering network security involves more than just knowing about protocols; it requires strategic implementation and continuous management. Organizations must:
- Regularly Update and Patch: Ensure all network devices and software using these protocols are kept up-to-date to mitigate known vulnerabilities.
- Strong Configuration: Implement protocols with strong encryption ciphers, robust authentication methods, and appropriate key lengths. Avoid default settings.
- Continuous Monitoring: Utilize network monitoring tools to observe protocol behavior, detect anomalies, and respond to potential threats in real-time.
- User Training: Educate users on the importance of secure practices, such as strong passwords and recognizing phishing attempts that target protocol-based authentication.
Frequently Asked Questions (FAQ)
Q1: What are the fundamental pillars of network security?
The fundamental pillars of network security are confidentiality, integrity, and availability (the CIA triad). Confidentiality ensures data privacy through encryption,