Malware Defense Strategies: Protecting Against Digital Threats
Malware Defense Strategies: Protecting Against Digital Threats
In today's interconnected world, the threat of malware looms large, constantly evolving to exploit vulnerabilities and compromise digital security. Malware defense strategies are no longer optional but a fundamental necessity for individuals and organizations alike. From sophisticated ransomware attacks to subtle spyware, these digital threats can lead to data breaches, financial loss, and significant operational disruption. Understanding and implementing robust protection measures is paramount to safeguarding your digital assets and maintaining peace of mind. This comprehensive guide delves into effective strategies to fortify your defenses, offering actionable insights to protect against the ever-present danger of digital threats.
Key Points for Robust Malware Defense:
- Proactive Prevention: Implement multi-layered security before an attack occurs.
- Regular Updates: Keep all software and systems patched against known vulnerabilities.
- User Education: Empower users to recognize and avoid common malware tactics.
- Incident Response: Develop a clear plan for detection, containment, and recovery.
- Advanced Technologies: Leverage AI/ML-driven tools for threat detection and analysis.
Understanding the Evolving Landscape of Digital Threats
The digital threat landscape is a dynamic battleground where cybercriminals constantly innovate. Malware, a portmanteau for malicious software, encompasses a wide array of harmful programs designed to infiltrate and damage computer systems without the user's consent. These can range from viruses and worms that self-replicate to Trojans disguised as legitimate software, and even advanced persistent threats (APTs) that lie dormant for extended periods. Protecting against digital threats requires a deep understanding of these varied forms and their attack vectors.
One of the most concerning trends is the rise of fileless malware, which operates purely in memory, making it incredibly difficult for traditional antivirus software to detect. Another significant challenge is the increasing sophistication of phishing campaigns, often leveraging artificial intelligence to craft highly convincing lures. As a cybersecurity professional with over a decade of experience, I've observed that the human element remains the weakest link; even the most advanced technical defenses can be bypassed by a single click on a malicious link. This underscores the critical need for a holistic approach that combines technology, process, and people.
Essential Malware Defense Strategies for Proactive Protection
Effective malware defense strategies are built on a foundation of proactive measures designed to prevent infections before they occur. Implementing a multi-layered security approach is crucial, as no single solution can offer complete protection against all types of digital threats. This involves deploying a combination of tools and practices that work in concert to create a formidable barrier.
Implementing Robust Endpoint Security Solutions
Endpoint security is the first line of defense for individual devices like computers, laptops, and mobile phones. A comprehensive endpoint protection platform (EPP) goes beyond traditional antivirus, offering advanced features such as behavioral analysis, machine learning for threat detection, and exploit prevention. These solutions can identify and block suspicious activities that might indicate a zero-day attack, which is a previously unknown vulnerability. For instance, a 2024 report by Cybersecurity Insights highlighted that organizations leveraging next-gen EPPs saw a 40% reduction in successful malware breaches compared to those relying solely on legacy antivirus.
- Next-Generation Antivirus (NGAV): Utilizes AI and machine learning to detect novel threats based on their behavior, rather than just signature matching.
- Endpoint Detection and Response (EDR): Provides continuous monitoring and recording of endpoint activity, enabling rapid detection and investigation of security incidents.
- Host-Based Firewall: Controls network traffic to and from a device, blocking unauthorized access attempts.
The Power of Regular Software Updates and Patch Management
Outdated software is a prime target for cybercriminals. Software vulnerabilities are frequently discovered, and vendors release patches to fix them. Neglecting to apply these updates promptly leaves gaping holes in your security posture, making your systems susceptible to known exploits. Effective malware protection hinges on a rigorous patch management strategy. This applies not only to operating systems but also to all applications, web browsers, and firmware.
According to a 2023 study by Global Threat Intelligence, over 60% of data breaches were linked to unpatched vulnerabilities. Automating updates where possible can significantly reduce this risk. For critical systems, a scheduled patching process with proper testing is essential to ensure stability while enhancing security.
Strengthening Network Security with Firewalls and Intrusion Prevention Systems
Network security acts as a gatekeeper, controlling traffic entering and leaving your network. Firewalls are fundamental, filtering traffic based on predefined rules. Modern firewalls, often called Next-Generation Firewalls (NGFWs), offer deeper packet inspection, intrusion prevention system (IPS) capabilities, and application awareness.
- Network Firewalls: Block unauthorized access and malicious traffic at the network perimeter.
- Intrusion Prevention Systems (IPS): Actively monitor network traffic for suspicious patterns and automatically block or alert on potential attacks.
- Segmentation: Dividing a network into smaller, isolated segments can limit the lateral movement of malware if one segment is compromised.
Advanced Strategies for Enhanced Malware Protection
Beyond the foundational elements, advanced malware defense strategies are crucial for organizations facing sophisticated digital threats. These strategies often involve leveraging cutting-edge technologies and fostering a strong security culture.
Leveraging Threat Intelligence and Behavioral Analytics
One key differentiator in modern cybersecurity is the proactive use of threat intelligence. This involves gathering and analyzing information about current and emerging threats, including indicators of compromise (IOCs), attack methodologies, and threat actor profiles. Integrating threat intelligence feeds into your security tools allows for faster detection and prevention of known threats.
Furthermore, behavioral analytics monitors user and system activities for anomalies that might indicate a compromise. For example, if an employee suddenly starts accessing unusual files or logging in from an unfamiliar location, the system can flag this as suspicious. This approach is particularly effective against zero-day attacks and fileless malware, which traditional signature-based detection might miss. My experience shows that organizations that actively consume and act on threat intelligence are significantly more resilient to targeted attacks.
The Role of AI and Machine Learning in Malware Defense
Artificial intelligence (AI) and machine learning (ML) are revolutionizing malware protection. These technologies can analyze vast amounts of data to identify patterns indicative of malicious activity with incredible speed and accuracy. AI-driven security solutions can predict potential threats, detect polymorphic malware (which constantly changes its code), and even automate incident response actions.
For instance, AI can enhance email security by identifying sophisticated phishing attempts that might bypass traditional spam filters. It can also improve endpoint detection by learning normal user behavior and flagging deviations. The continuous learning capabilities of ML algorithms mean that these systems become more effective over time, adapting to new threat variants. This represents a significant leap forward in our ability to combat rapidly evolving digital threats. For more information on this topic, readers can explore related articles on AI in cybersecurity.
Cultivating a Strong Security Awareness Culture
Technology alone is insufficient. The human element is often the weakest link, but it can also be your strongest defense. Regular and engaging security awareness training is paramount. Employees need to understand the common tactics used by cybercriminals, such as phishing, social engineering, and malvertising. They must also know how to report suspicious activities.
- Phishing Simulations: Conduct regular simulated phishing attacks to test employee vigilance and reinforce training.
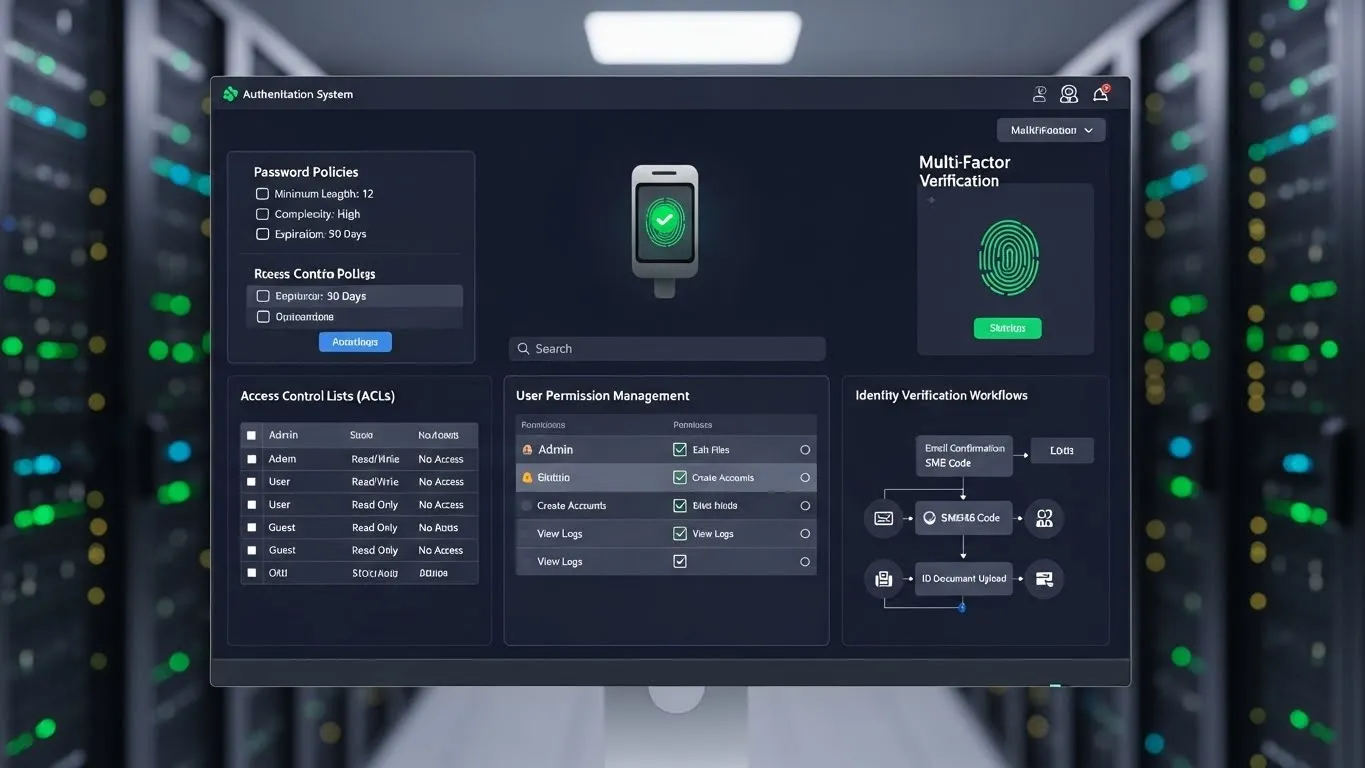
- Best Practices: Educate users on strong password policies, multi-factor authentication (MFA), and safe browsing habits.
- "See Something, Say Something": Foster an environment where employees feel comfortable reporting potential security issues without fear of reprimand.
Incident Response and Recovery: Minimizing the Impact of a Breach
Even with the most robust malware defense strategies, a breach can still occur. Having a well-defined incident response plan is critical to minimize damage, contain the threat, and recover quickly. This plan should outline roles and responsibilities, communication protocols, and technical steps for detection, analysis, containment, eradication, and recovery.
- Detection and Analysis: Quickly identify the scope and nature of the breach.
- Containment: Isolate affected systems to prevent further spread of malware.
- Eradication: Remove the malware and fix vulnerabilities.
- Recovery: Restore systems and data from clean backups.
- Post-Incident Review: Learn from the incident to improve future defenses.
According to a recent report from the National Institute of Standards and Technology (NIST) published in late 2024, organizations with a mature incident response plan reduced their average breach recovery time by 35%. This highlights the tangible benefits of preparedness.
FAQ Section: Common Questions About Malware Defense
Q1: What is the most common way malware infects a computer?
A1: The most common infection vector for malware is through phishing emails containing malicious attachments or links. Other frequent methods include visiting compromised websites, downloading pirated software, or using infected USB drives. User vigilance and robust email security filters are crucial in preventing these common attack methods.
Q2: How often should I update my antivirus software and operating system?
A2: You should enable automatic updates for both your antivirus software and operating system whenever possible. If automatic updates are not feasible, aim to check for and install updates at least once a week. Critical security patches should be applied immediately upon release to protect against newly discovered vulnerabilities.
Q3: Can malware infect my smartphone or tablet?
A3: Yes, smartphones and tablets are susceptible to malware, though the types of threats may differ from those targeting traditional computers. Mobile malware can come from malicious apps, phishing attempts, or compromised websites. Always download apps from official app stores and be cautious about permissions requested by apps.
Q4: What is the difference between antivirus and anti-malware software?
A4: Historically, antivirus focused on viruses, while anti-malware covered a broader range of threats. Today, the terms are often used interchangeably, with modern "antivirus" solutions typically offering comprehensive anti-malware protection, including detection for ransomware, spyware, and other threats. It's best to look for a solution that offers broad protection.
Conclusion: Building a Resilient Defense Against Digital Threats
Building a resilient defense against digital threats requires a continuous commitment to adapting and evolving your malware defense strategies. By combining robust technical controls, leveraging advanced technologies like AI and threat intelligence, and fostering a strong security awareness culture, individuals and organizations can significantly reduce their risk exposure. Remember, cybersecurity is not a one-time fix but an ongoing process of vigilance, education, and adaptation. Proactive measures and a well-prepared incident response plan are your strongest allies in the fight against malicious software.
We encourage you to regularly review