Implementing Strong Authentication: Preventing Unauthorized Access
Implementing Strong Authentication: Preventing Unauthorized Access
In an increasingly interconnected digital landscape, the threat of unauthorized access poses a significant risk to individuals and organizations alike. Data breaches, identity theft, and system compromises often stem from weak authentication mechanisms. Implementing strong authentication is no longer an option but a critical imperative for safeguarding sensitive information and maintaining operational integrity. This article explores the fundamental principles, modern techniques, and best practices for establishing robust authentication systems, ensuring that only authorized users gain entry, thereby preventing unauthorized access effectively.
Key Points:
- Foundation of Security: Strong authentication is the bedrock of any robust cybersecurity strategy.
- Multi-Factor Authentication (MFA): Essential for adding layers of defense beyond simple passwords.
- Passwordless Future: Exploring biometrics and FIDO2 for enhanced user experience and security.
- Adaptive Security: Utilizing context-aware authentication to detect and block suspicious logins.
- Zero Trust Integration: Aligning authentication with a broader security philosophy for comprehensive protection.
The Imperative of Strong Authentication in Today's Digital World
The digital realm is constantly under siege from sophisticated cyber threats. From phishing attacks to credential stuffing, adversaries relentlessly target weak entry points to gain unauthorized access. A single compromised account can lead to catastrophic data breaches, financial losses, and severe reputational damage. This makes implementing strong authentication a non-negotiable component of any effective cybersecurity posture. It serves as the primary gatekeeper, verifying user identities before granting access to valuable resources. Without it, even the most advanced firewalls and intrusion detection systems can be bypassed if an attacker simply acquires valid login credentials.
Organizations, especially those operating in the cloud, face unique challenges. The distributed nature of cloud environments means that traditional perimeter-based security is insufficient. Identity becomes the new perimeter, making robust identity verification paramount for preventing unauthorized access. According to a 2024 industry report by CyberSecure Insights, over 60% of data breaches in the past year involved compromised credentials, highlighting the urgent need for stronger authentication methods.
Understanding the Core Principles of Strong Authentication
Strong authentication moves beyond the simplicity of a single password by requiring multiple pieces of evidence to verify a user's identity. These pieces typically fall into three categories:
- Something You Know: This includes traditional passwords, PINs, or security questions. While foundational, these are often the weakest link due to user habits (reusing passwords) and vulnerability to social engineering.
- Something You Have: This refers to physical tokens like smart cards, hardware security keys (e.g., YubiKey), or even a mobile phone receiving a one-time password (OTP) via SMS or an authenticator app. This factor significantly raises the bar for attackers.
- Something You Are: This category encompasses biometric data, such as fingerprints, facial recognition, or iris scans. Biometrics offer a high level of convenience and security, as they are inherently unique to the individual.
By combining at least two of these distinct factors, strong authentication creates a layered defense that is far more resilient to attacks than single-factor methods. This multi-layered approach is crucial for preventing unauthorized access even if one factor is compromised.
Key Technologies for Implementing Strong Authentication
Modern strong authentication relies on a suite of advanced technologies to deliver both security and user experience.
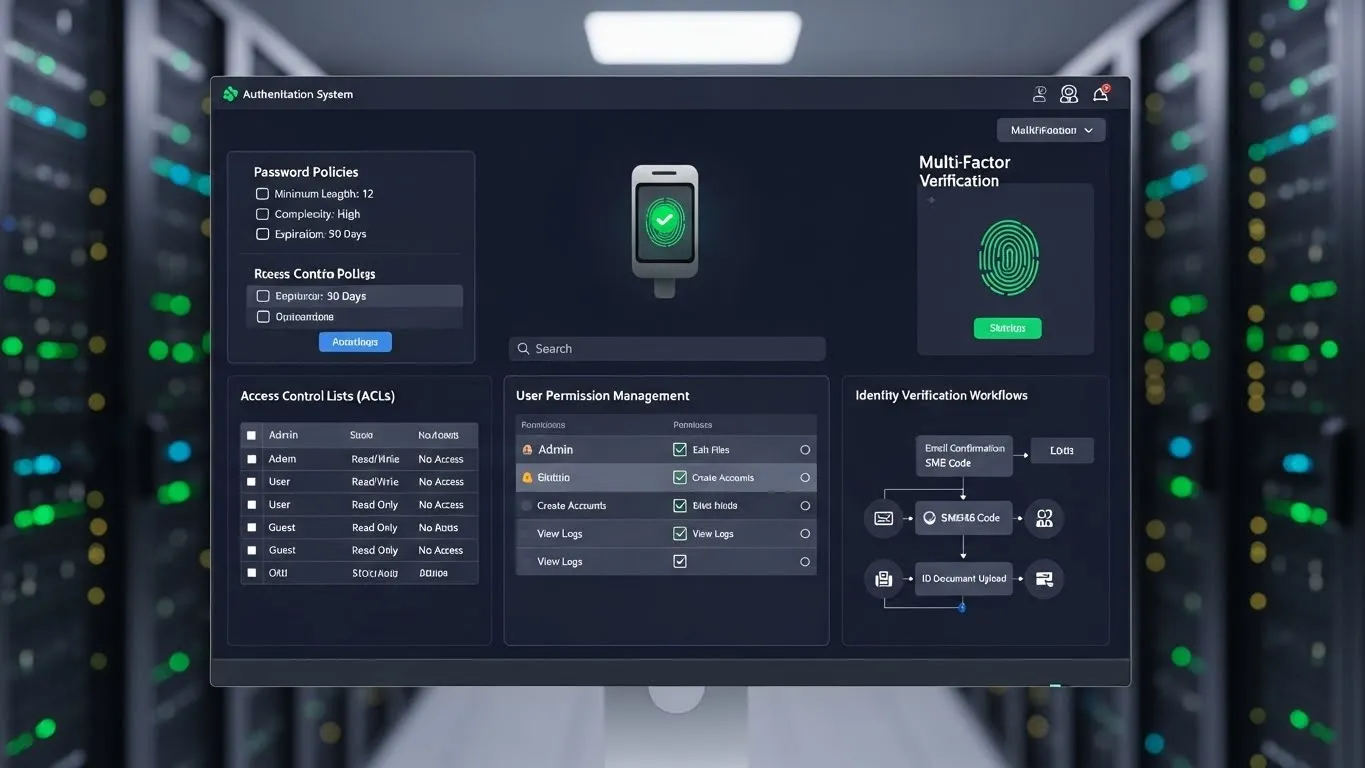
Multi-Factor Authentication (MFA)
MFA is the most widely adopted form of strong authentication. It requires users to provide two or more verification factors to gain access.
- SMS-based OTPs: While convenient, SMS can be vulnerable to SIM-swapping attacks.
- Authenticator Apps: Apps like Google Authenticator or Microsoft Authenticator generate time-based one-time passwords (TOTPs) and are generally more secure than SMS.
- Hardware Security Keys (FIDO2/WebAuthn): These physical devices offer the strongest protection against phishing and man-in-the-middle attacks. They leverage public-key cryptography to verify identity.
- Biometrics: Integrated into many devices, biometrics like fingerprint or facial recognition provide a seamless and secure MFA experience.
Passwordless Authentication
The future of authentication is increasingly moving towards passwordless solutions, which eliminate the need for traditional passwords altogether. This not only enhances security by removing the weakest link but also improves user convenience.
- Biometric Login: Direct login using fingerprints, facial scans, or voice recognition.
- Magic Links/Email Verification: A temporary, single-use link sent to a registered email address.
- FIDO2 and WebAuthn: These open standards enable strong, phishing-resistant authentication using hardware security keys or built-in platform authenticators (like Windows Hello or Touch ID). A 2023 report from the FIDO Alliance highlighted a significant reduction in credential theft for organizations adopting FIDO2.
Adaptive and Context-Aware Authentication
Adaptive authentication dynamically assesses risk factors during a login attempt and adjusts the authentication requirements accordingly. This is a highly differentiated approach to preventing unauthorized access.
- Location-Based: If a login attempt comes from an unusual geographic location, additional verification might be requested.
- Device Recognition: Recognizing trusted devices and prompting for extra authentication on new or unrecognized devices.
- Behavioral Biometrics: Analyzing user behavior patterns (typing speed, mouse movements) to detect anomalies.
- Time-Based: Flagging logins outside of typical working hours.
This intelligent approach significantly enhances security by identifying and challenging potentially fraudulent login attempts in real-time.
Best Practices for Implementing Strong Authentication
Successfully implementing strong authentication requires more than just deploying technology; it demands a holistic strategy.
1. Prioritize User Experience and Education
Security measures should not hinder productivity. Choose authentication methods that balance security with ease of use. Crucially, educate users on the importance of strong authentication, how to use it, and how to identify phishing attempts. Regular training sessions can significantly reduce human error, a common cause of security incidents.
2. Adopt a Zero Trust Security Model
Integrating strong authentication into a Zero Trust framework is a powerful strategy for preventing unauthorized access. In a Zero Trust model, no user or device is inherently trusted, regardless of their location inside or outside the network. Every access request is verified. Strong authentication, especially MFA, becomes a cornerstone of this "never trust, always verify" philosophy. For more information on this topic, readers can explore related articles on identity and access management and Zero Trust principles.
3. Leverage Cloud-Native Security Features
For cloud environments, utilize the robust identity and access management (IAM) services provided by cloud providers (e.g., AWS IAM, Azure AD, Google Cloud IAM). These platforms offer built-in MFA, conditional access policies, and integration with enterprise directories, simplifying the process of implementing strong authentication at scale. A recent study by Cloud Security Alliance (2025) emphasized that organizations fully leveraging cloud-native security features experience 30% fewer identity-related breaches.
4. Regular Audits and Updates
Authentication systems are not "set it and forget it." Regularly audit authentication logs for suspicious activity, review access policies, and update authentication methods as new threats emerge or technologies improve. This proactive approach is vital for maintaining an effective defense against evolving cyber threats.
Challenges and Solutions in Strong Authentication Deployment
While the benefits are clear, deploying strong authentication can present challenges:
- Legacy Systems: Integrating modern authentication with older, proprietary systems can be complex.
- Solution: Implement API gateways or identity brokers to bridge the gap, allowing legacy systems to leverage modern authentication protocols without extensive re-engineering.
- User Adoption: Resistance to change or perceived inconvenience can hinder adoption.
- Solution: Focus on user-friendly options like biometrics or single sign-on (SSO) with MFA. Provide clear communication on benefits and comprehensive support.
- Cost and Complexity: Initial investment in hardware or software, and ongoing management.
- Solution: Start with high-risk accounts and gradually expand. Leverage cloud-based identity services to reduce infrastructure costs and management overhead.
FAQ Section
Q: What is the most secure form of strong authentication available today? A: Hardware security keys utilizing FIDO2/WebAuthn standards are widely considered the most secure. They use public-key cryptography to create phishing-resistant credentials, making them extremely difficult for attackers to compromise. When combined with biometrics, they offer an excellent balance of security and convenience, significantly enhancing protection against sophisticated attacks.
Q: Can strong authentication prevent all types of unauthorized access? A: While strong authentication significantly reduces the risk, no single security measure can prevent all types of unauthorized access. It is a critical component but must be part of a broader security strategy that includes secure coding practices, regular vulnerability assessments, endpoint protection, and robust access control policies. Human factors like social engineering can still pose a risk.
Q: How often should authentication methods be reviewed and updated? A: Authentication methods and policies should be reviewed at least annually, or more frequently if there are significant changes in the threat landscape, regulatory requirements, or organizational structure. Regular audits ensure that the chosen methods remain effective against emerging threats and align with current best practices. Staying proactive is key to maintaining a strong security posture.
Q: Is passwordless authentication truly more secure than traditional passwords with MFA? A: Yes, in many cases, passwordless authentication can be more secure. It eliminates the weakest link in the security chain—the