Effective Threat Prevention Techniques: Proactive Cybersecurity Measures
The digital landscape is constantly evolving, presenting new and sophisticated threats to individuals and organizations alike. Implementing effective threat prevention techniques is no longer optional but a critical imperative for maintaining security and operational continuity. This article delves into proactive cybersecurity measures designed to fortify your defenses against a myriad of cyber threats, from malware and ransomware to advanced persistent threats. We'll explore strategies that move beyond reactive responses, focusing instead on anticipating and neutralizing potential dangers before they can cause harm. Understanding and applying these measures can significantly reduce your attack surface and protect valuable data.
Key Points:
- Proactive Defense: Shift from reactive to anticipatory security strategies.
- Layered Security: Implement multiple defense mechanisms for comprehensive protection.
- Continuous Monitoring: Stay vigilant with ongoing threat detection and analysis.
- Employee Education: Empower users as the first line of defense.
- Regular Updates: Keep systems and software patched against known vulnerabilities.
Understanding the Evolving Digital Threat Landscape
The nature of cyber threats is dynamic, with attackers constantly refining their methods. What worked as a defense strategy five years ago may be insufficient today. Organizations face an increasing volume of sophisticated attacks, including highly targeted phishing campaigns, zero-day exploits, and fileless malware. This complex environment necessitates a fundamental shift from merely reacting to incidents to adopting proactive cybersecurity measures.
Common Cyber Threats Today
Today's threat landscape is dominated by several pervasive dangers. Ransomware continues to be a significant concern, encrypting critical data and demanding payment, often disrupting business operations for extended periods. Phishing attacks remain a primary vector for initial compromise, tricking users into revealing credentials or downloading malicious software. Furthermore, advanced persistent threats (APTs) pose a long-term risk, as attackers stealthily infiltrate networks to exfiltrate data over time. Understanding these common threats is the first step in developing robust defenses.
The Shift Towards Proactive Cybersecurity
Traditionally, many security strategies focused on detection and response after a breach occurred. However, the cost and damage associated with breaches have driven a move towards prevention. Proactive cybersecurity involves anticipating potential attacks, identifying vulnerabilities before they are exploited, and implementing safeguards to block threats at their earliest stages. This approach emphasizes continuous vigilance and a layered defense strategy, aiming to stop threats before they can impact systems or data.
Foundational Effective Threat Prevention Techniques
Building a strong cybersecurity posture begins with implementing several foundational techniques. These measures form the bedrock of any robust defense strategy and are essential for safeguarding digital assets. Neglecting these basics leaves significant gaps for attackers to exploit.
Robust Endpoint Security Solutions
Every device connected to your network, from laptops and servers to mobile phones, represents a potential entry point for attackers. Endpoint security solutions are critical for monitoring and protecting these individual devices. Modern endpoint detection and response (EDR) systems go beyond traditional antivirus, offering advanced capabilities like behavioral analysis, threat hunting, and automated response. Implementing a comprehensive EDR solution is a cornerstone of effective threat prevention techniques, providing visibility and control over your entire device ecosystem.
Implementing Strong Network Security
Network security measures are designed to control access to your network and protect its infrastructure. This includes deploying firewalls, intrusion detection/prevention systems (IDPS), and secure network configurations. Segmenting your network into smaller, isolated zones can significantly limit the lateral movement of attackers if a breach occurs in one segment. For more information on this topic, readers can explore related articles on network segmentation best practices. Regularly reviewing and updating network security policies is vital to counter evolving threats.
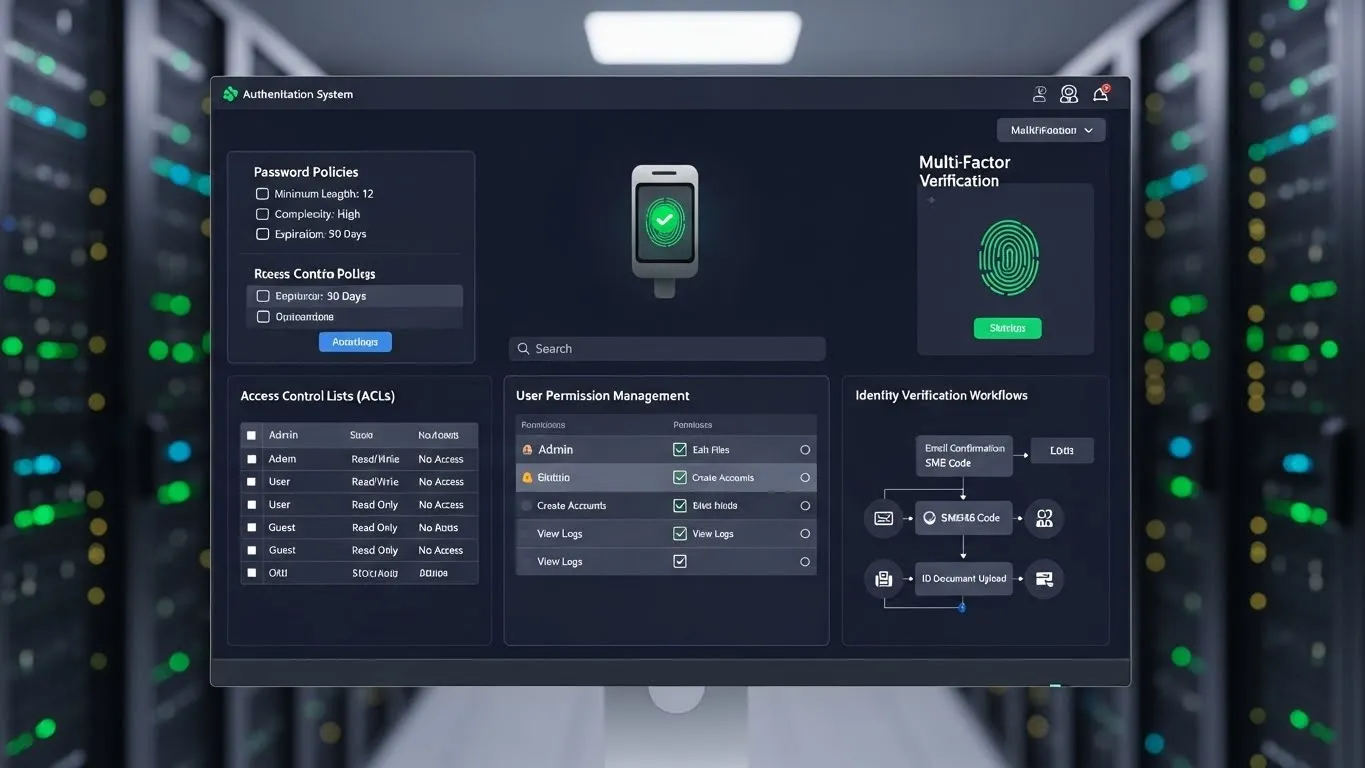
Data Encryption and Access Control
Protecting data, both in transit and at rest, is paramount. Data encryption renders information unreadable to unauthorized parties, even if they manage to access it. Implementing strong access control mechanisms, such as multi-factor authentication (MFA) and the principle of least privilege, ensures that only authorized individuals can access sensitive data. Zero-trust principles dictate that no user or device should be trusted by default, regardless of their location within or outside the network, demanding verification for every access attempt.
Advanced Proactive Cybersecurity Measures
Beyond the foundational elements, advanced techniques offer deeper layers of protection, leveraging cutting-edge technologies to stay ahead of sophisticated adversaries. These measures are increasingly important for organizations facing high-stakes cyber risks.
AI-Powered Threat Detection and Behavioral Analytics
Artificial intelligence (AI) and machine learning (ML) are revolutionizing threat detection. These technologies can analyze vast amounts of data to identify subtle anomalies and patterns indicative of malicious activity that human analysts might miss. Behavioral analytics focuses on understanding normal user and system behavior, flagging deviations as potential threats. For instance, a user suddenly accessing unusual files or logging in from an unfamiliar location could trigger an alert. AI-driven security tools provide predictive capabilities, enhancing effective threat prevention techniques.
Zero-Trust Architecture: A Modern Approach
As mentioned, Zero-Trust is a security model built on the principle of "never trust, always verify." It assumes that threats can originate from anywhere, both inside and outside the network perimeter. Every access request, regardless of its origin, is authenticated, authorized, and continuously validated. Implementing a Zero-Trust architecture involves micro-segmentation, strong identity verification, and continuous monitoring of all network traffic. According to a 2023 report by Forrester, organizations adopting Zero-Trust principles reported a significant reduction in data breach impact. This approach is a powerful way to enhance proactive cybersecurity measures.
Security Awareness Training and Phishing Simulation
Even with the most advanced technological defenses, humans remain a common target for cyberattacks. Security awareness training educates employees about common threats like phishing, social engineering, and malware. Regular training, coupled with simulated phishing campaigns, helps employees recognize and report suspicious activities, turning them into a strong line of defense rather than a vulnerability. Our experience shows that consistent, engaging training significantly reduces the click-through rate on malicious emails.
The Role of Timely Updates and Incident Response
Maintaining security is an ongoing process that requires continuous attention to system health and preparedness for potential breaches. Two critical components of this are diligent patch management and a well-defined incident response plan.
Patch Management and Vulnerability Scanning
Software vulnerabilities are frequently discovered, and attackers are quick to exploit them. Timely patch management ensures that all operating systems, applications, and firmware are updated with the latest security fixes. Regular vulnerability scanning helps identify unpatched systems and misconfigurations before attackers can find them. This proactive approach significantly reduces the attack surface and is a fundamental aspect of effective threat prevention techniques. Organizations should aim for automated patch deployment where possible to ensure consistency.
Developing a Comprehensive Incident Response Plan
Despite the best prevention efforts, no system is 100% impenetrable. A comprehensive incident response plan outlines the steps an organization will take before, during, and after a security incident. This includes identification, containment, eradication, recovery, and post-incident analysis. A well-rehearsed plan minimizes damage, reduces recovery time, and helps an organization learn from incidents. For insights into developing a robust plan, consider exploring articles on incident response frameworks.
Differentiated Insights: Emerging Trends in Threat Prevention
Staying ahead of cyber adversaries requires an understanding of emerging trends and innovative solutions. Two areas currently gaining significant traction offer unique advantages in threat prevention.
Supply Chain Security Focus
Recent high-profile attacks have highlighted the critical vulnerability of the software supply chain. Attackers are increasingly targeting third-party vendors or components used in software development to compromise a wider array of end-users. Enhanced supply chain security involves rigorous vetting of vendors, continuous monitoring of third-party software, and implementing secure development practices. Organizations are now demanding greater transparency from their suppliers regarding their security postures, a crucial differentiated point in modern threat prevention. A 2025 report by the Cybersecurity & Infrastructure Security Agency (CISA) emphasized the need for a "whole-of-ecosystem" approach to supply chain risk.
The Rise of XDR for Unified Visibility
Extended Detection and Response (XDR) is an evolution of EDR, offering a unified security incident detection and response platform that automatically collects and correlates data across multiple security layers – including endpoints, networks, cloud, and email. This provides a much broader and deeper view of potential threats than traditional point solutions. XDR platforms leverage AI and automation to accelerate threat detection, investigation, and response. Implementing XDR provides unparalleled visibility, allowing security teams to identify and neutralize complex, multi-stage attacks more effectively, marking a significant advancement in proactive cybersecurity measures.
FAQ Section
Q: What is the primary difference between reactive and proactive cybersecurity?
A: Reactive cybersecurity focuses on detecting and responding to threats after they have occurred, often mitigating damage post-breach. Proactive cybersecurity, conversely, aims to anticipate and prevent threats before